Principles of composition/aggregation reuse
The Composite/Aggregate Reuse Principle (CARP) is generally called the Composite Reuse Principle (CRP), which is defined as: try to use composite/aggregate instead of inheriting to achieve the purpose of reuse. The principle of composition/aggregation reuse is to use some existing objects in a new object to make it a part of the new object; the new object achieves the purpose of reusing existing functions by delegating to these objects held internally. Instead of getting existing functions th...
1. Salt
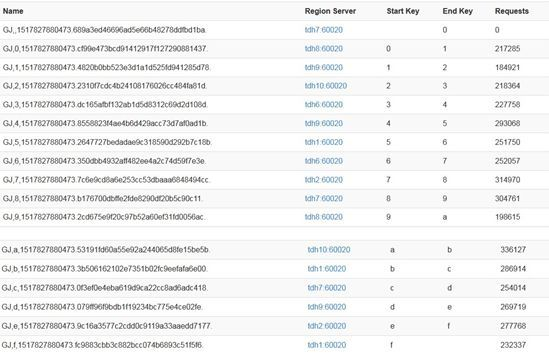
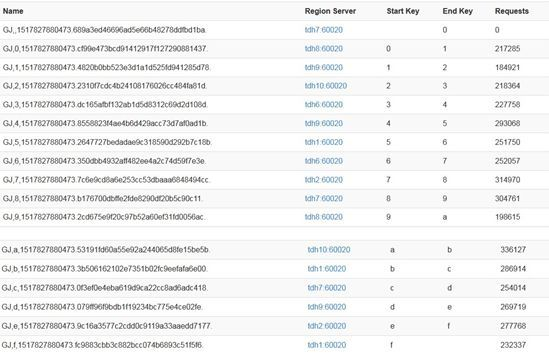
The application of Salting in HBase is to assign a random character to each rowkey prefix, so that the data is scattered in multiple different regions to achieve a balanced load. If the table region in HBase is distinguished according to the prefix of each letter, let's compare the changes before and after adding salt to the rowkey. First, we give a set of rowkeys before salt: rk001 rk002 rk003 According to the partition, the above rowkey is in the same region. Below we add salt to the above ...
Significance of the Single Responsibility Principle
The single responsibility principle tells us: a class cannot do too many things. In a software system, the more responsibilities a class (a module, or a method) assumes, the lower the possibility of it being reused. A very typical example is the universal class. In fact, we can tell the truth: any conventional MVC project, in extreme cases, can use one class (or even one method) to complete all functions. But doing so will cause serious coupling and even affect the whole body. A class underta...
https://rss3.bio/0x8fC645e6a176F07395B8f44196d1443772FE9d57
Principles of composition/aggregation reuse
The Composite/Aggregate Reuse Principle (CARP) is generally called the Composite Reuse Principle (CRP), which is defined as: try to use composite/aggregate instead of inheriting to achieve the purpose of reuse. The principle of composition/aggregation reuse is to use some existing objects in a new object to make it a part of the new object; the new object achieves the purpose of reusing existing functions by delegating to these objects held internally. Instead of getting existing functions th...
1. Salt
The application of Salting in HBase is to assign a random character to each rowkey prefix, so that the data is scattered in multiple different regions to achieve a balanced load. If the table region in HBase is distinguished according to the prefix of each letter, let's compare the changes before and after adding salt to the rowkey. First, we give a set of rowkeys before salt: rk001 rk002 rk003 According to the partition, the above rowkey is in the same region. Below we add salt to the above ...
Significance of the Single Responsibility Principle
The single responsibility principle tells us: a class cannot do too many things. In a software system, the more responsibilities a class (a module, or a method) assumes, the lower the possibility of it being reused. A very typical example is the universal class. In fact, we can tell the truth: any conventional MVC project, in extreme cases, can use one class (or even one method) to complete all functions. But doing so will cause serious coupling and even affect the whole body. A class underta...
https://rss3.bio/0x8fC645e6a176F07395B8f44196d1443772FE9d57
Share Dialog
Share Dialog

Subscribe to rojeck

Subscribe to rojeck
<100 subscribers
<100 subscribers
Using hash to assign randomly, a given row can have the same origin when it is salted. Locally, this disperses the grip between RegionServers and allows prediction during read operations. The deterministic hash (deterministic hash) can reconstruct the complete row key on the client side, and can use the get operation to directly obtain the desired row.
For example, after processing the above three row keys (unsalted), here we use the MD5 hash algorithm, and the results are as follows
f18a79a8eb39267173fd0d113e3282f4
277ba32a1610268cdb7733192010c127
bd1258481401ea1be6377c5aaeae3a1f
Design rule: MD5+main dimension+dimension identifier+sub-dimension 1+time dimension+sub-dimension 2
For example: MD5 top four digits of seller ID + seller ID + app + first-level catalog + date + second-level catalog
Using the first four digits of MD5 as the first part of the rowkey, the data can be hashed to balance the server load and avoid hot issues. The seller ID is required for query, which narrows the scope of our scan and can query the data we need faster.
Finally, the length of the rowkey will also affect our performance. Since HBase is a columnar database, if the length of the rowkey is doubled, the overall storage capacity will increase exponentially. Therefore, the design of rowkey does not have a fixed pattern. In actual practice, we need to refer to various factors to achieve the optimization of rowkey.
Using hash to assign randomly, a given row can have the same origin when it is salted. Locally, this disperses the grip between RegionServers and allows prediction during read operations. The deterministic hash (deterministic hash) can reconstruct the complete row key on the client side, and can use the get operation to directly obtain the desired row.
For example, after processing the above three row keys (unsalted), here we use the MD5 hash algorithm, and the results are as follows
f18a79a8eb39267173fd0d113e3282f4
277ba32a1610268cdb7733192010c127
bd1258481401ea1be6377c5aaeae3a1f
Design rule: MD5+main dimension+dimension identifier+sub-dimension 1+time dimension+sub-dimension 2
For example: MD5 top four digits of seller ID + seller ID + app + first-level catalog + date + second-level catalog
Using the first four digits of MD5 as the first part of the rowkey, the data can be hashed to balance the server load and avoid hot issues. The seller ID is required for query, which narrows the scope of our scan and can query the data we need faster.
Finally, the length of the rowkey will also affect our performance. Since HBase is a columnar database, if the length of the rowkey is doubled, the overall storage capacity will increase exponentially. Therefore, the design of rowkey does not have a fixed pattern. In actual practice, we need to refer to various factors to achieve the optimization of rowkey.
No activity yet